Shopping Girl Retro 30s Cartoon Rubber Hose Style" iPad Case & Skin for Sale by skullislandprod | Redbubble

What is a side channel attack? How these end-runs around encryption put everyone at risk | CSO Online

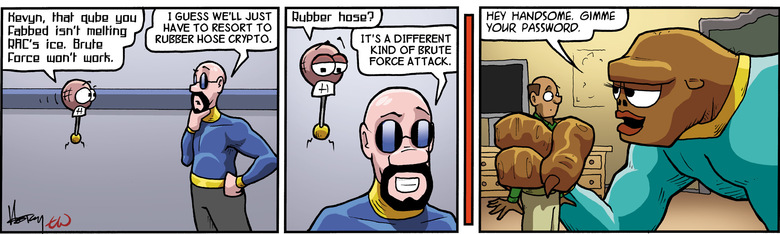
טוויטר \ Peter Leimbigler בטוויטר: "@austwitnerd @ZachWeiner Conventionally known as rubber-hose cryptanalysis, which is very computationally inexpensive: https://t.co/ZpxKVWWQBh"

Bathroom Hand Held Spa Shower Head Round Nozzle Ultra thin Boost Chrome Shower Head Bathroom Shower Accessories|Shower Heads| - AliExpress

Amazon.com: Pipe Fittings Accessories 1.5M Copper Core Shower Hose Adjustable Water Flow Steel Encryption Lightweight Handheld Hose Bathroom Shower Head Hose : Tools & Home Improvement
Can't send PGP message that is encrypted, but not signed, since 5.200 · Issue #1961 · thundernest/k-9 · GitHub